Fencer covers the full application security stack: static code analysis, dynamic testing, dependency scanning, and secrets detection. Up and running in minutes, no security team required.
Fencer scans your source code on every pull request and on a daily schedule, surfacing security vulnerabilities before they reach production. Findings appear inline in your PR — in GitHub, GitLab, or Bitbucket — so developers fix issues in the same workflow they already use.
%20(1).avif)
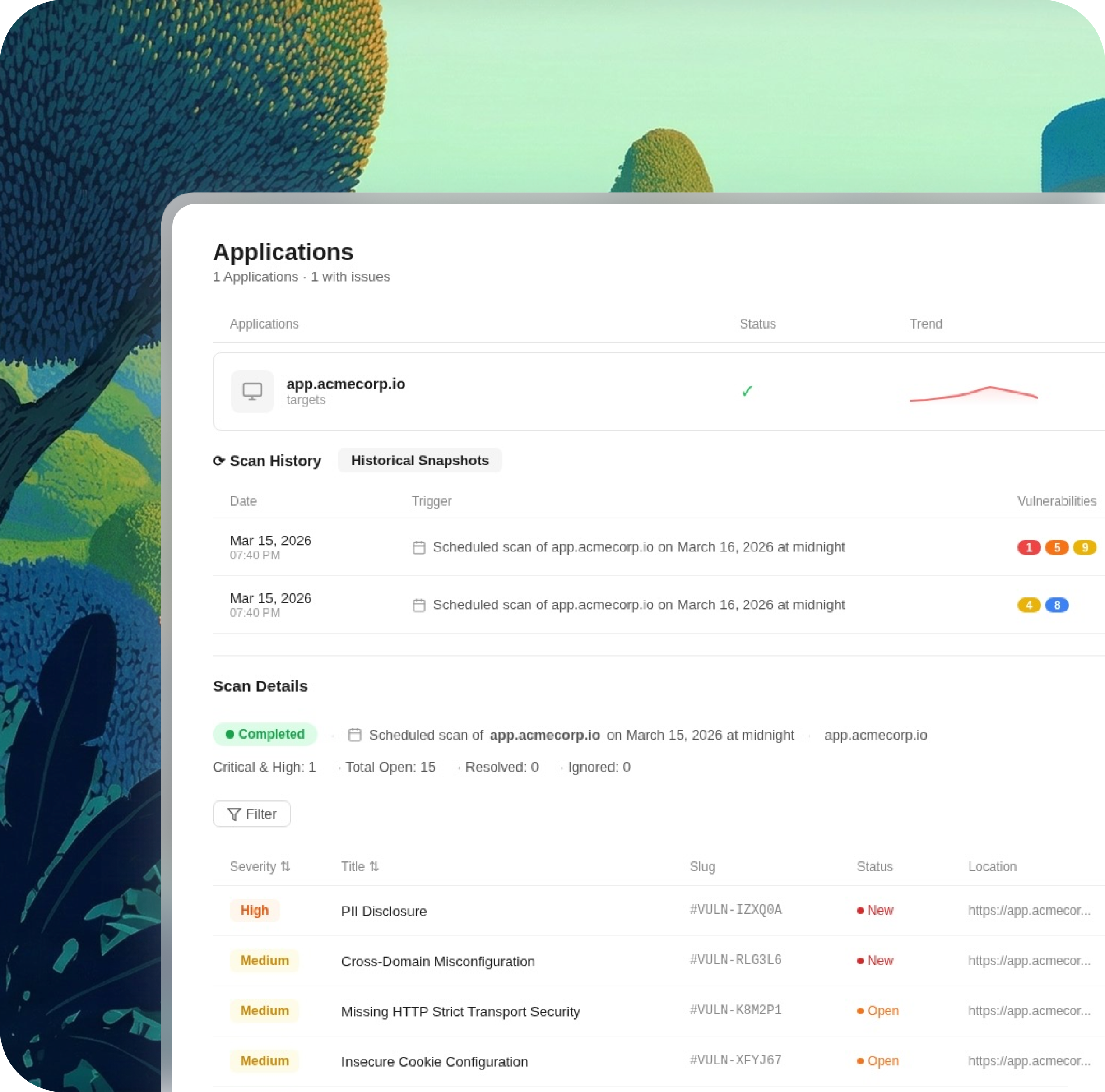
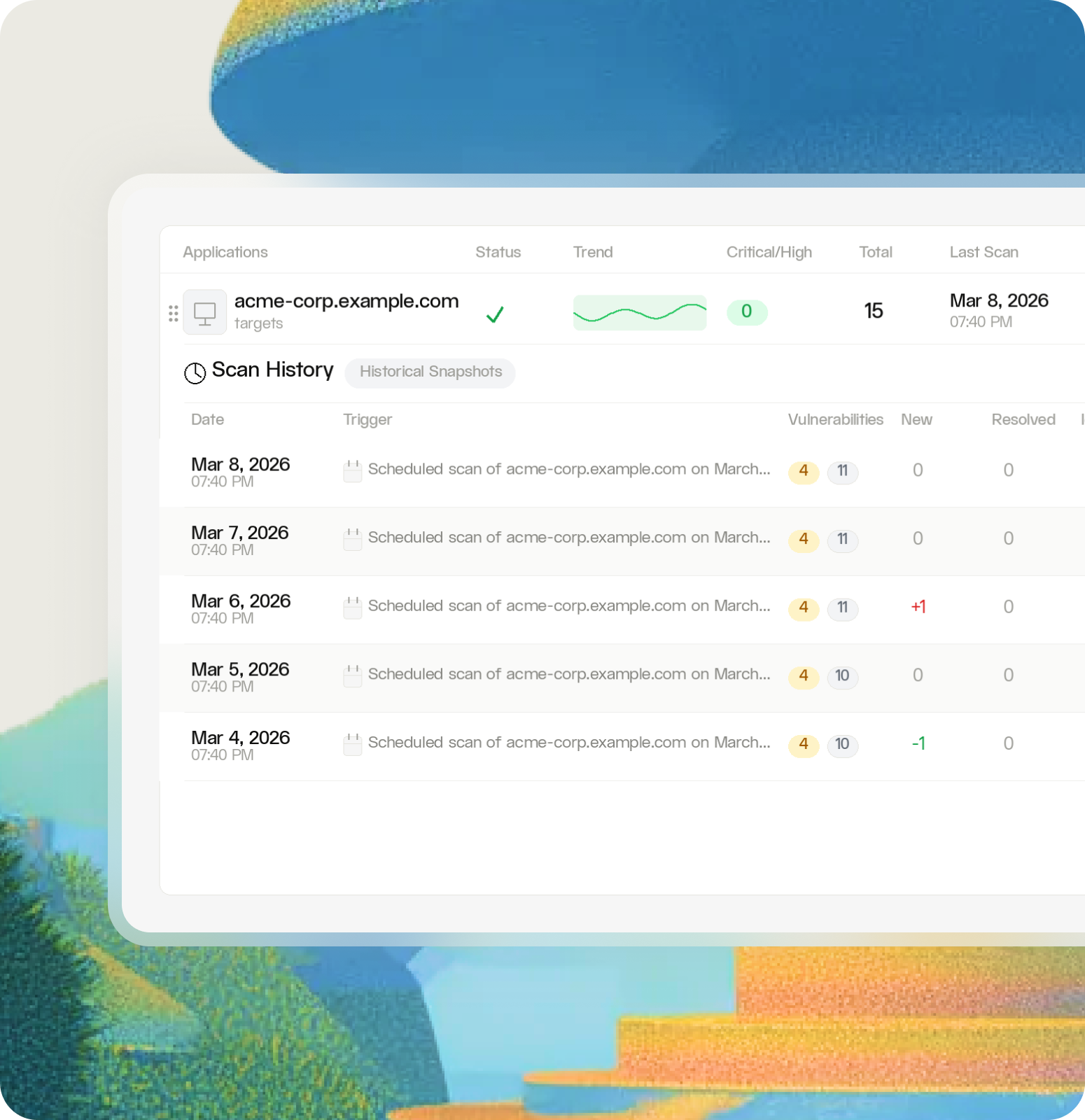
DAST finds runtime vulnerabilities such as SQL injection, cross-site scripting, broken authentication, and more. Fencer tests your application, APIs, and MCP servers on a continuous schedule, so your coverage keeps pace with your shipping cadence rather than waiting for the next pen test.
Fencer scans your code repositories and hosting platforms for exposed secrets such as API keys, tokens, credentials, and private keys.
.html.png)
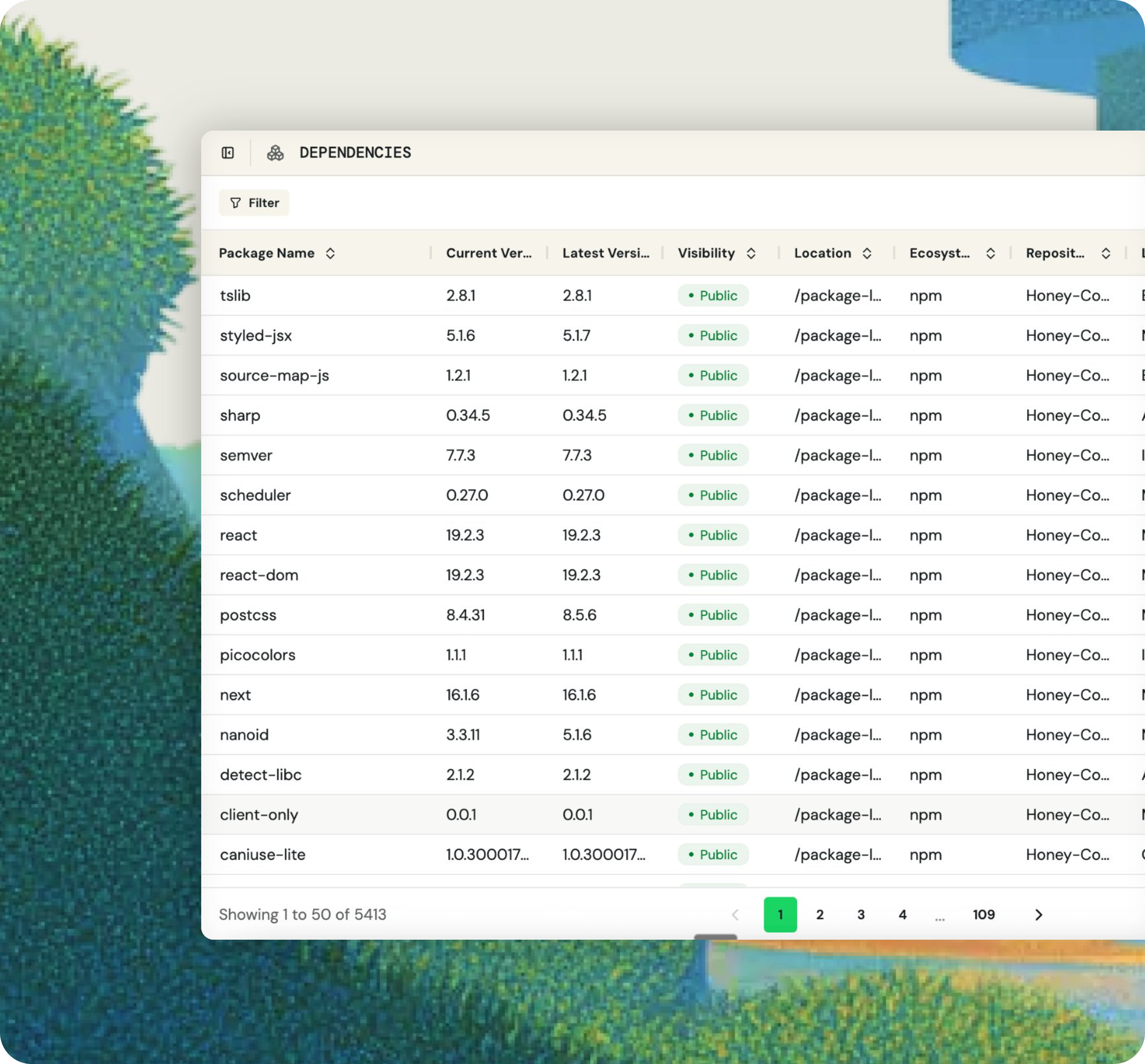
Fencer inventories every open source package across your connected repositories and surfaces known vulnerabilities, license risks, and outdated packages. When a new CVE drops, you know immediately which repos are affected and how severe the exposure is — before you read about it somewhere else.
Dependabot, a SAST tool, a separate DAST scanner: managing three tools that generate separate alerts in separate dashboards with no shared context is a full-time job. Fencer consolidates all four application security disciplines into one platform with one unified finding view.
SOC 2 auditors want evidence of continuous vulnerability scanning, not a pen test report from last year. Fencer generates a timestamped record of every scan, finding, and resolution automatically and sends it to your GRC tool.
Pen tests are valuable, but finding a critical vulnerability during an annual test means it was there all year. Fencer runs continuously so issues surface when they're introduced, not 11 months later.

— Ben Papillon
CTO & Co-founder, Schematic